SQRL-ing Mnemonic Phrases

Authored by Gregory
How a simple technique can help you add a layer of security to your hardware wallet
When it comes to digital wallets, there are two basic types: hot wallets and cold wallets. Hot wallets are easy-to-use applications connected to the internet (think MetaMask or Exodus). In contrast, cold wallets (sometimes called cold storage) are not connected to the internet and are typically hardware devices like a Ledger or Trezor.
Deciding how to allocate your funds between the two types is a personal choice based on your need for security vs. functionality. And while most people are aware that cold wallets are safer, it's not hard, even for experienced users, to become complacent.
While using a cold wallet is advisable, it doesn't guarantee safety. And many users take hardware wallets for granted, assuming they are much more reliable and secure than a browser extension. But in this case, safer doesn't mean perfect.
If you choose to use a hardware wallet, generally, this means that you and you alone are in control of your private keys. This is a big responsibility, and unfortunately, the weakest link in almost all cases is the user and how they manage their mnemonic phrase or "secret words."
A quick aside for anyone who isn't familiar, these "secret words" are what's often referred to as a "seed" or "recovery" phrase - the master key generated by your wallet. If you'd like to learn more about these keys and how they're created, here's a great resource.
When it comes to hardware wallets, problems often stem from secret word mismanagement. One way to defend against these issues is by using a technique introduced by RicMoo called Simultaneous Qualified Roots with Lure or SQRL, which anyone can use to secure their hardware wallet devices further.
What is SQRL-ing?
While most crypto users are familiar with the random 12 or 24-word phrases mentioned above, fewer know that they can include a mystical 13th or 25th word. And importantly, this extra word can act as an additional layer of security.
Let me break this down further. When wallet software ingests a set of secret words, they use fancy math called "salting" and "hashing" to generate user accounts. This is true for both public and private keys, and it's done in a deterministic fashion, so you'll always get the same result.
Because of how this process works, a user can apply a password that gets salted and hashed with the rest of the secret words. Simply put, we can add another word to the set of secret words to get a different set of accounts.
The result is having two sets of secret words, one with 24 words and another with 25 words. And this allows you to place funds into this second set of accounts, like a squirrel burying an acorn for the winter.
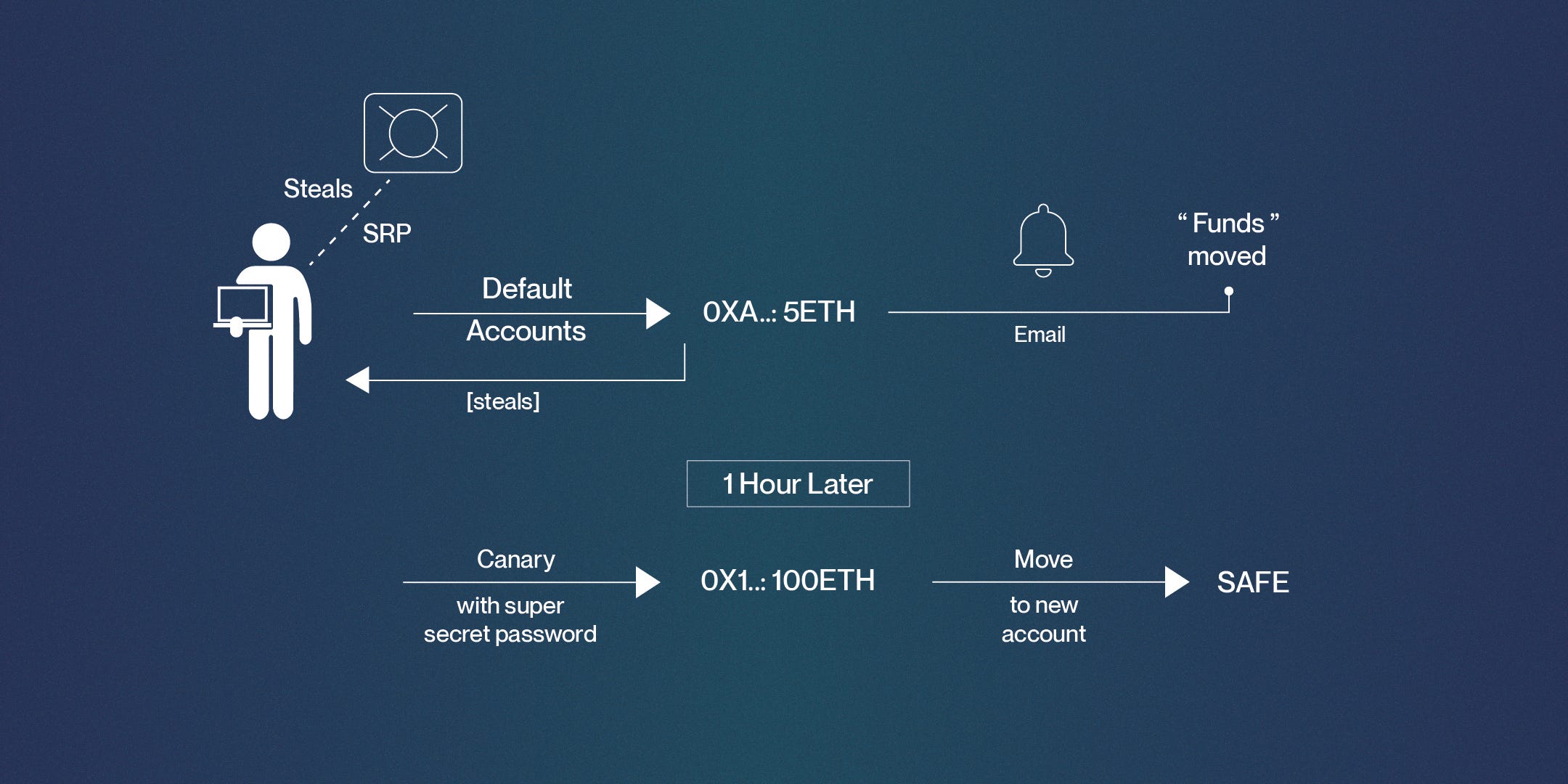
Here's how this looks.
SQRL-ing in practice
Historically, miners would place canaries in various parts of a coal mine to help detect poisonous gasses, and if the bird died, the mine was evacuated. Similarly, SQRL-ing can enhance your security system by enabling a "canary" account. That is, using your secret words as a canary account designed to detect problems, while the secret words + password account holds your main funds.
To work properly, the canary account must have something of value - for instance, a nominal amount of ETH or another crypto asset that you're willing to lose. Think of this as a small insurance policy to protect your main holdings.
Let's say your secret words become compromised. Someone robs your house and takes a piece of paper containing your secret words from your sock drawer. When they enter the secret words, that will grant them access to your canary account and not your main funds because they don't know the extra password.
At this point, the attacker would need to assume you have other holdings and try to guess your password. But more than likely, they'll see the default account has funds and immediately steal them, not realizing that what they're doing is taking the bait and alerting you that your secret words have been leaked.
It's also essential to set up email alerts (etherscan or similar services) anytime funds are transferred out of your canary account. That way, you'll know right away if your secret words have been compromised, and hopefully, the password should deter the hacker from accessing your funds, buying you enough time to get your funds to safety. Should that happen, you need to immediately rotate your funds into a newly SQRL'd account and stop using those secret words.
How to SQRL on a Ledger
There are two ways to SQRL on a Ledger, using the "Attach to Pin" method or setting a temporary passphrase." To keep things simple, we'll focus only on Attach to Pin. Set temporary passphrase will be covered in a future article.
Attach to Pin
Similar to how the Ledger device secures your secret words with a pin, you can secure the passphrase with a pin. This allows you to unlock your ledger device with either of the two pins (the original pin you used during setup or the newly created pin).
NOTES:
-
They must be different pins. I have no idea what would happen if you set them the same. I can only imagine pure chaos.
-
You cannot use the
Attach to Pinfeature multiple times. Each time you set up a pin, it will remove the previous one from memory.
Attach to Pin
-
Unlock the device.
-
While on the dashboard (where you select an app), navigate to the Ledger device settings by holding both buttons simultaneously until the screen changes.

- Open the ‘settings' application.

- Open the ‘security' settings.

- Navigate to and select the ‘passphrase' settings option.

- There will be some warnings, navigate to the final screen, and select ‘setup passphrase.'

- Select ‘Attach to PIN.'

-
Enter your pin of choice. Note, this is not your passphrase. This pin is used to encrypt/decrypt the passphrase.
-
Pick a passphrase that you feel is secure, it might be advised to use a password generator, or you could pick a complex set of characters.
It's extremely important to make a copy of this passphrase and store it safely because if your Ledger device resets, you will not be able to recover these accounts. Treat this passphrase with equal security as your secret words.
Note: You have three types of characters to choose from, lowercase letters, uppercase letters, and special characters (such as question marks, commas, etc.). The passphrase is case-sensitive.
- You'll be required to confirm your pin. Once you've done that, it's time to choose a passphrase. This screen can be tricky to navigate. Play around with it a little bit. Just make sure to delete everything when you're ready.

- Once you've entered your passphrase, you'll see an option to confirm the passphrase. Navigate to the next window until you see ‘confirm passphrase.'

-
You'll be asked to confirm your pin. This is the pin that you've unlocked the Ledger with. This is simply a security measure.
-
You'll see a screen that says ‘processing,' and once it's done, it should say ‘passphrase set.'


-
To use the new passphrase, you'll need to unplug or lock your device and re-enter the new PIN.
-
Test and verify that you see a new set of accounts with your favorite application of choice (MyCrypto, MetaMask, etc.).
-
Now you can unlock your device with your original PIN or the newly created one protecting your passphrase!
Useful articles:
Passphrase: Ledger's Advanced Security Feature
Ledger's guide on using passphrases
Acknowledgments:
This article was inspired by SQRL-ing Mnemonic Phrases By RicMoo.
About ChainSafe
ChainSafe is a leader in blockchain development and infrastructure solutions for Web3. We're supporting the multi-chain future by building client implementations for Ethereum, Filecoin, Polkadot, and Mina. We're also maintaining the Web3.js library, working on a gaming SDK that connects NFTs to Unity, building a decentralized cloud storage application, and bootstrapping a multi-chain bridging protocol. To learn more, click here.
Want to help build the foundations of Web3? Join us!
Have a question, comment, or suggestion? Drop into our Discord and join the conversation! We're also always looking for talented people. Check out our open positions and get in touch ➡️➡️ careers@chainsafe.io