The 2026 Guide to Blockchain Privacy: 5 approaches for institutional adoption
Blockchain privacy has moved from ideology to architecture. Explore privacy approaches, from ZK-Rollups and private L2s to TEEs and FHE, shaping institutional digital asset management in 2026.

Disclaimer: ChainSafe maintains Lodestar (Ethereum), serves as a Super Validator for the Canton Network, and runs validator nodes for Aztec and zkVerify.
In the rapidly evolving blockchain landscape, choosing the right privacy architecture is crucial for institutional adoption. 2026 is seeing a direct emphasis on the versatility of real-world asset tokenization (RWA's), and some of the most significant forays by legacy finance into blockchain technology to date.
While "institutional finance" and "decentralized finance" have long been separated by furrowed brows and long pauses, the leaps in privacy-enabled blockchain technology of the 2020's have begun to bear fruit. Tokenized assets are being positioned as the next influx of onchain capital despite the regulatory uncertainty of the day.
This guide explores five approaches best suited for various institutional digital asset management needs in 2026.
From ideology to architecture
Looking back, 2025 will be remembered as the year the blockchain industry finally traded its "privacy ideology" for "privacy architecture." For years, the conversation was dominated by the choice between total transparency and total anonymity. However, these discussions, fueled by the rapid rise of ZK-as-a-Service and the institutional push of the Canton Network, shifted the hype away from hiding data and toward its sophisticated management.
We are moving past the era of experimental "dark pools" and entering the age of institutional confidentiality. The goal for institutions isn't to obscure the ledger, but to ensure that sensitive data remains visible on a need-to-know basis.
Now firmly in 2026, the dust from those debates has given way to a mature, multi-chain reality. Decision-makers are no longer distracted by the "ZK-everything" or the siloed promises of early enterprise chains. Instead, they are navigating a landscape defined by cryptographic agility and selective disclosure.
Whether leveraging the programmable privacy of Ethereum’s ZK-Rollups or the composable confidentiality of the Canton Network, the focus for blockchain implementation for institutions has shifted to Best Fit for Purpose.
This guide serves as a primer on the available privacy frameworks in 2026, offering a roadmap for those who need to protect institutional assets without sacrificing regulatory compliance or liquidity.
Key takeaways for 2026
- Privacy layers are essential for scaling institutional operations on public blockchains.
- Each privacy method offers unique benefits and trade-offs; the choice depends on your organization's specific needs.
- Understanding the basics of each can help guide strategic investments without requiring deep technical expertise.
Ethereum (Public ZK-Rollups): Scalability Meets Privacy-as-a-Service
Best For: Institutions needing to enhance scalability while offering optional privacy layers.
ZK-Rollups provide a means to achieve scalability on Ethereum by bundling multiple transactions into a single transaction, improving throughput and reducing fees. Their "Privacy-as-a-Service" offerings enable customizable privacy layers for various use cases.
Pros:
- Scalability: Efficient transaction bundling reduces costs and increases speed.
- Flexibility: Modular privacy layers adapt to specific privacy needs.
Considerations:
- Complexity of Integration: Requires careful planning to integrate privacy layers without disturbing existing workflows.
- Ecosystem Dependence: Being strongly tied to Ethereum, it may be subject to its network limitations and advancements.
Aztec Network: The "Private World Computer"

Aztec is establishing itself as the premier private-by-default Layer 2 on Ethereum. Unlike traditional rollups that are transparent until told otherwise, Aztec treats confidentiality as a foundational property.
It uses a Hybrid State model that allows public and private smart contracts to interact seamlessly. You can keep your internal trade logic and balances entirely encrypted while settling on the public Ethereum ledger.
Aztec uses a specialized language called Noir to simplify the creation of Zero-Knowledge proofs, allowing non-engineers to oversee programmable privacy rules. An example rule might be: ensuring a trade is compliant without revealing the participants.
ZKsync: The Institutional Hyperchain Gateway

ZKsync has matured into a massive ecosystem of Hyperchains: interoperable ZK-chains tailored to specific institutional needs.
ZKsync uses a "Privacy-on-Demand" design. While its main Era network is transparent, institutions can deploy their own modular Hyperchains that use validiums to store data off-chain. This keeps sensitive transaction data within an organization's own firewalls while the "proof" of the transaction is verified on Ethereum.
offers the most "enterprise-friendly" path to privacy, allowing firms to choose exactly where their data sits (data residency) while benefiting from the shared liquidity of the broader ZKsync ecosystem.
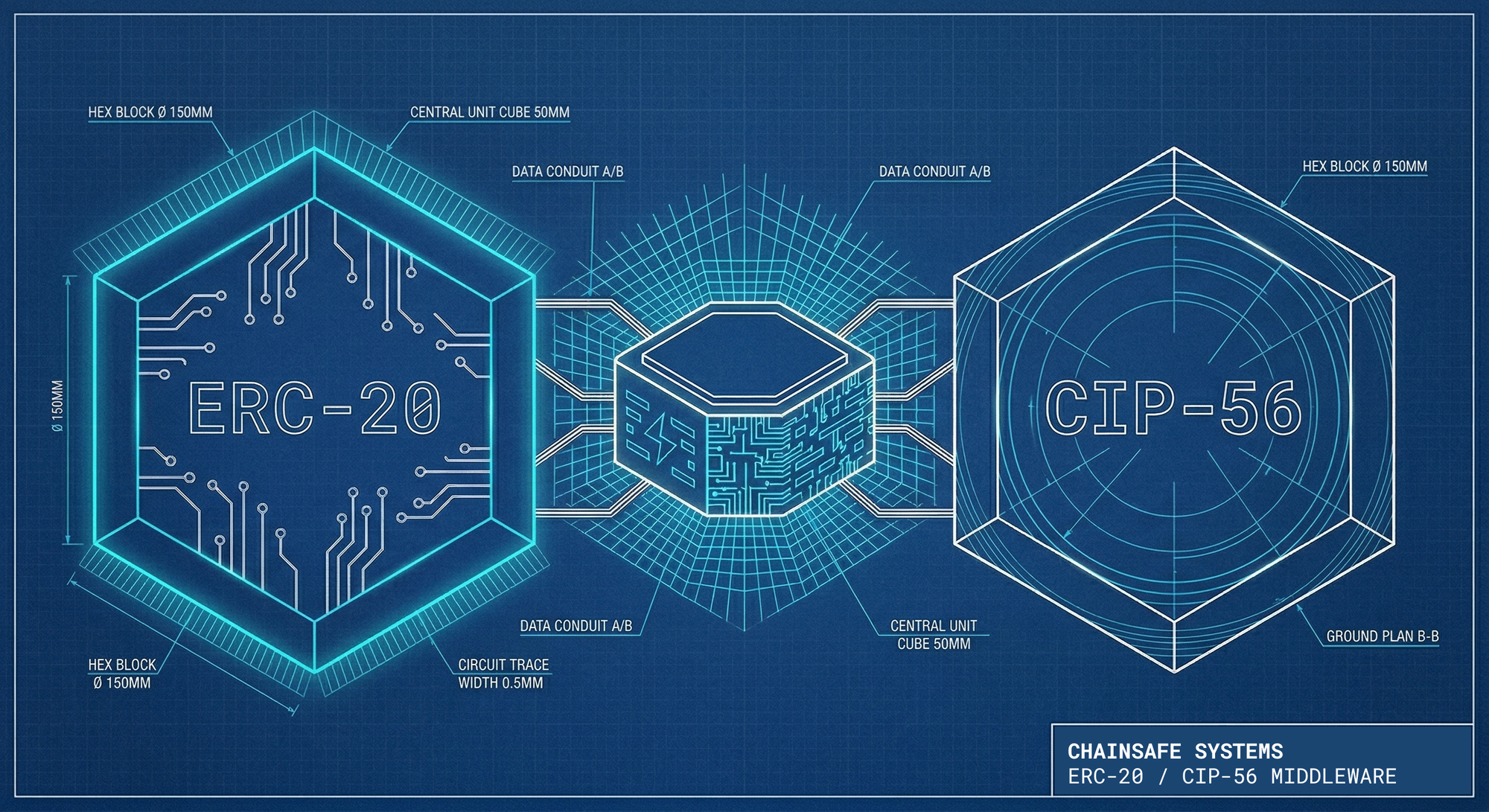
zkVerify: The Universal Proof Verification Layer

zkVerify is best for projects that need to drastically reduce the high cost of privacy without sacrificing security or being locked into a single ecosystem.
In the 2026 landscape, the bottleneck of blockchain privacy isn't just generating the data, it’s the expensive process of verifying it on a public ledger like Ethereum. zkVerify serves as a specialized, high-performance highway for Zero-Knowledge (ZK) proofs, acting as a dedicated "verification-as-a-service" layer that offloads this burden from more expensive networks.
zkVerify is a specialized Layer 1 designed exclusively to check the math behind privacy proofs. Instead of an institution spending massive amounts in gas fees to verify a proof on Ethereum, they submit it to zkVerify. The network confirms the proof is valid in under a second and then sends a lightweight "attestation" back to the main chain.
Whether an institution is using Aztec’s encryption, ZKsync’s hyperchains, or even custom STARK-based systems, zkVerify can handle them all. This gives entities a degree of versatility in their infrastructure design, allowing them to swap their underlying privacy technology in the future without rebuilding their entire verification infrastructure.

Canton Network: Composability with Confidentiality

Best For: Complex institutional workflows requiring composability with embedded confidentiality features.
Canton Network uses a "Privacy-by-Design" method. It is made to fit current rules in legacy finance systems.
In 2026, the Canton Network advanced its position as an institutional Ledger. While many privacy solutions focus on the individual user, Canton focuses on the interconnectedness of institutional systems. It utilizes a unique architecture that allows independent blockchains (built on the Daml smart contract language) to connect into a unified network while maintaining strict data silos.
Canton’s approach differs from the standards set by existing public blockchains, leveraging what's called a synchronization protocol. It allows atomic transactions (where multiple steps either happen simultaneously or not at all) across different organizations. For example, a repo trade involving a bank in London and a custodian in New York can settle instantly. However, only the participants in that specific trade can see the transaction details. The rest of the network remains unaware that the exchange even occurred.

Pros:
- Tailored Workflows: Efficient for intricate, cross-platform institutional processes.
- High Confidentiality: Built-in privacy at the protocol level ensures confidentiality across transactions.
Considerations:
- Vendor Lock-in: Relies heavily on the network’s own ecosystem for maximum benefit.
- Ecosystem Barrier: Maximum utility is reached when counterparties are also on the Canton Network, creating a "walled garden" effect for certain digital asset classes.
- Interoperability Challenges: May face hurdles in integrating with non-Canton applications.

Zero-Knowledge Proofs (ZKP): Verification without Revelation
Best For: Proving compliance, solvency, or identity without exposing the underlying sensitive spreadsheets.
In 2026, Zero-Knowledge Proofs (ZKPs) have moved from academic curiosities to the standard "API of Trust." They function as a mathematical envelope: you can prove what is inside the envelope satisfies a rule (e.g., "I have the funds for this trade") without ever opening it.
In institutional finance, ZKPs are now used primarily for Selective Disclosure. An institution can provide a "Proof of Reserves" to a regulator every ten minutes without revealing its specific portfolio holdings or trade secrets. This "Verification without Revelation" allows firms to participate in public DeFi liquidity pools while keeping their proprietary strategies encrypted.
Zero-Knowledge Proofs allow parties to prove knowledge of a fact without disclosing the fact itself, making them ideal for privacy-sensitive transactions.
Pros:
- Absolute Privacy: No data is shared, only the truth of the data.
- Efficiency: Once generated, proofs are lightweight and can be settled on public chains like Ethereum for a fraction of the cost of traditional auditing.
Considerations:
- Computation Costs: While 2026 hardware accelerators have helped, proving complex multi-party trades still requires significant server-side power.
Trusted Execution Environments (TEEs): Hardware-Based Privacy
Best For: Scenarios demanding high security through hardware-enforced privacy.
TEEs use hardware-level security to safely handle sensitive data inside a set environment. This reduces the chance of outside threats.
As we look at the 2026 tech stack, Trusted Execution Environments (TEEs) such as Intel SGX and AWS Nitro represent the hardware-based alternative to ZKPs. Think of a TEE as a "black Box" inside a computer's processor. Data is encrypted, decrypted, and processed inside the secure enclave, and the result is sent out encrypted. Even the person owning the computer cannot see what is happening inside the chip.
For institutions, TEEs are a strong choice for confidential computing. When a ZKP is too computationally expensive to generate (such as running a complex risk-assessment model), a TEE can do it in milliseconds. In 2026, many Privacy-as-a-Service providers use a hybrid model: TEEs for speed and ZKPs for the final, permanent record on the blockchain.
Pros:
- High Performance: Processes data at near-native speeds, making it ideal for real-time institutional trading.
- Versatility: Can handle any type of code, not just that written for specific cryptographic circuits.
Considerations:
- Hardware Trust: You must trust the chip manufacturer (e.g., Intel or AMD) and the physical security of the data center.
- Maintainability: Dependent on vendor support for updates and security patches.
Fully Homomorphic Encryption (FHE): Encryption in processing
Best For: Performing complex computations on highly sensitive datasets, such as dark pools or credit scoring, without compromising secrecy.
Fully Homomorphic Encryption allows data to remain encrypted while being processed, offering robust privacy. This method has transitioned from theory to a functional reality for specialized institutional use cases. While ZKPs prove that a computation is correct, FHE allows you to actually perform that computation on encrypted data. This means a third-party service provider can process your sensitive trade data or client info without ever seeing the raw numbers.
In the context of 2026 digital asset management, FHE is primarily utilized for private outsourcing. Institutions can send encrypted transaction batches to a high-performance cloud or a shared liquidity pool. The pool can execute logic, such as matching a buy order with a sell order, on the ciphertexts themselves. The result is returned to the institution, which is the only party capable of decrypting the final outcome. It creates a powerful "zero-trust" relationship between data owners and data processors.
Pros:
- Ultimate Privacy: Data remains encrypted in transit, at rest, and in use. Even a total breach of the processing server yields nothing but "digital noise" to an attacker.
- Reduced Data Breach Risks: Since the service provider never holds the decryption keys, the institutional liability for data leaks is virtually eliminated.
Considerations:
- Performance Overhead: Despite massive strides in "FHE-accelerated" chips in 2025, it remains the most computationally expensive privacy method, often requiring 10x to 100x more power than standard processing.
- Operational Complexity: Implementing FHE requires a deep bench of specialized cryptographic talent and a complete rethink of how data pipelines are structured.
Choosing the right privacy solution
The emphasis on blockchain privacy that emerged in the early 2020s has concluded not with a single winner, but with a mosaic of specialized solutions.
The mandate for institutional adoption is clear: Architecture is Strategy.
Choosing a privacy framework is no longer a purely technical decision; it is a risk management and liquidity decision. If you value the hardware-backed speed of TEEs, the mathematical certainty of ZKPs, or the institutional access of the Canton Network, your choice will shape how your firm works in an increasingly open digital economy.
The most successful firms of this era are those that remain cryptographically agile, ensuring that as these technologies mature, their digital assets remain secure, compliant, and, above all, private.
About ChainSafe
ChainSafe is a leading blockchain research and development firm specializing in protocol engineering, infrastructure development & operations, and co-development.
ChainSafe creates solutions for developers and teams across web3. As part of our mission to build accessible, improved tooling for developers, ChainSafe embodies an open source, community-guided ethos to advance the future of the internet.